SIM card fraudsters device ways of conning Kenyans

“My SACCO FOSA accounts were swept clean. I lost over Ksh90, 000 in a flash. Whoever was behind the criminal back-end activity proceeded to withdraw everything I had on the SACCO FOSA account via MPESA. They also emptied my MPESA account and borrowed Fuliza mobile loans on the line to my maximum limit as at the time. They moved airtime worth Ksh5, 000, which I had in Safaricom SIM card at the time.”
Ruth Kamau, Cyber Crime Victim
By Gor Ogutu
They hired a lawyer. Then armed him with a whopping Ksh900, 000 in bribe money, all in an attempt to buy off detectives working on the case to drop the charges and let them walk scott-free.
What they were unaware of, however, is the fact top state security organs have been spoiling for any chance to crack open what has now turned into a criminal enterprise stealing billions of shillings from the economy annually in electronic money fraud.
They are smooth operators. Except they are no Robbin Hoods. They steal from everyone including the poor. They steal from banks. They steal from the government. They have stolen millions from individuals – and lately, from firms and organizations.
Even after investing millions in cyber security defense systems, banks, mobile money transfer service providers and individuals remain defenseless and exposed, always at the mercy of modern day digital electronic money fraudsters armed with nothing but back-end knowledge of ICT systems operations.
In Kenya, the weakening of the economy during Covid-19 pandemic season has caused an unprecedented wave of unemployment. Online and in the realm of telecommunication networks, fraudsters saw an opportunity to strike. They are sleek and they are sophisticated.
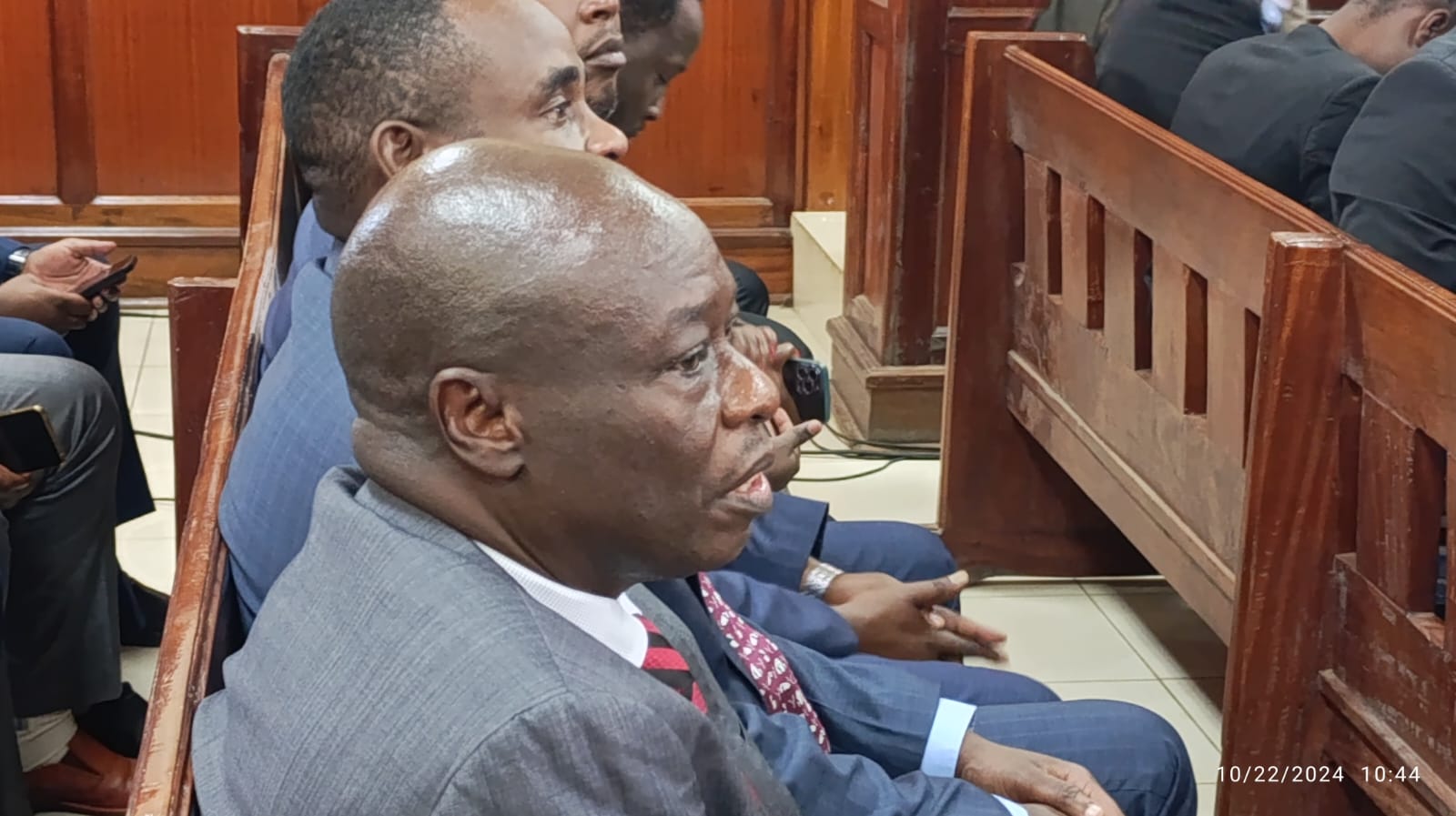
On Thursday August 13 this 2020, the lawyer for one such organised cell of electronic money fraudstars Mr. Antony Kirunyu Karoki; a practicing advocate at a Nairobi-based law firm, was arrested by Directorate of Criminal Investigations (DCI) detectives based at Kasarani.
He had been actualizing the attempt described earlier to bribe Kasarani Sub-County Criminal Investigations Officer with Ksh. 900,000 in an attempt to secure unconditional release of five suspects of electronic money fraud, without any charges.
Just the day before on August 12 2020, DCI detectives based at Kasarani had arrested five individuals within Pavab apartments on suspicion of engaging in electronic money fraud acting on a tip off from members of the public.
Samuel Githinji Njenga, Wilson Mugo Githinji, James Gitonga Maina, John Ngotho Kariuki and Ian Mbogo Kamau were found in possession of 1,720 unregistered Safaricom lines, 429 Airtel Lines, Five hand sets and five laptops, according to an official report by the DCI.
The five suspects were in possession of both registered and unregistered Safaricom subscriber lines among other electronic gadgets, and were being processed for arraignment in Court when the lawyer now turned suspect showed up.
Their lawyer, Mr. Antony Kirunyu Karoki came calling at the police station in Kasarani where they were being held, bearing hundreds of thousands of shillings in crisp bank notes in Ksh 1,000 denomination, unaware they would become DCI Scenes of Crime evidence against him shortly.
The money was promptly taken away as exhibit upon his arrest, with the suspect placed in custody awaiting to be charged with several offenses under the Bribery Act No. 47 of 2016 and the Penal Code.
Barely a month before on Monday July 20, 2020, DCI detectives arrested Safaricom employee Maurice Musoti & a JKUAT 4th year engineering student Rian Nyagaka for involvement in SIM Swap fraud, underscoring suspicions that criminal insider elements are now working in cahoots with electronic money fraudsters to steal from the public.
The two were found with a MacBook laptop, two thousand one hundred and sixty unused Safaricom SIM cards, forty four used Safaricom SIM cards, five MPESA till Agent numbers, Three MPESA Safaricom transaction recording books and an Internet Router.
For Ruth Kamau (not her real name) these arrests were too little too late, three weeks late to be exact. She had already suffered the most painful and traumatizing experience of her lifetime at the hands of electronic money fraudsters.
In the midst of a raging global pandemic, and the subsequent curfew restrictions that followed, late in the month of June 2020, and with her employer having asked staff to work from home unless summoned to complete tasks at the office, Ruth Kamau was at home in the City of Nairobi using the home Wi-Fi when late evening that particular Saturday the Wi-Fi suddenly ran out of subscription.
She would then opt to make one fatal phone call from whose subsequent events she is yet to recover, financially and emotionally.
Ruth recounts to this writer how, on that Saturday evening upon realizing her Wi-Fi subscription had run out, she placed a call to the customer care department of Safaricom, her Wi-Fi and mobile phone service provider and the leading mobile phone service provider in Kenya, asking a customer care agent on the other end of the line for modalities of paying up for a reconnection.
Like many City residents, she had recently signed up for home Wi-Fi from Safaricom. A few minutes after this call, Ruth says she received a call from a strange number – one which she could identify as a landline emanating from within Kenya.
“It was a landline number and the caller on the other end said they were calling from the Customer Care department of Safaricom based around Sarit Centre. The strange caller said another client had called the customer care service claiming ownership of my sim card,” Ruth Kamau narrates amid anguish.
“The strange caller on the landline said they were calling me so as to help them reconcile the database from their end with an aim of establishing the authenticity and true ownership of the SIM card line,” she says.
However, like every woke Nairobian, something occurred to Ruth that she was about to get conned, an instinct she now wishes she could have trusted.
“The caller kept insisting that if I did not trust him I could go to any nearby customer care Centre or MPESA money transfer shop to verify if the information they were telling me was true or false,” says Ruth.
On 27th March, 2020 President Uhuru Kenyatta announced a nationwide dusk-to-dawn curfew in Kenya to contain the spread of the coronavirus pandemic. Later on, on April 5, 2020, these orders were strengthened further by the announcement of cessation of movement into and out of a number of areas across the country .
Up until late June 2020 when this strange caller came for Ruth, the dusk to dawn curfew restrictions were still in place before they were eventually lifted on July 6. Public service vehicles were also out of operations from early in the evening, and so were taxis.
It was now past 5PM in the evening, and Ruth, knowing too well customer care offices would probably be closed if she ever made it there in time before commencement of the curfew, abandoned any thoughts of visiting a customer care office that evening, as the caller on the line was suggesting, opting instead to engage the strange caller to try find a solution.
She listened on to this supposed-to -be ‘’customer care agent”, requesting to know what exactly they wanted to verify. To her shock and dismay, the person on the other end of the line correctly read out to her information pertaining to her private and confidential information “like they were reading it out from the back-end of an ICT system,” she says.
“The caller corroborated all my ID and PIN codes for the sim card and even read out the fact that they could see in the system I was a registered owner of a home Wi-Fi,” Ruth Kamau recollects.
The caller also informed Ruth of personal details of her mobile money Personal Identification (PIN) numbers: The PIN she had originally been using when she bought the SIM card and the new one she had altered in a bid to step up the security of the SIM card.
“A spiral of events then followed in quick succession. The caller asked me which mobile money PIN number I preferred to retain of the two, and I indicated which one before they moved on to the SIM card PIN number which was also changed after they read out the one I was presently using from the back-end,” says Ruth.
She narrates how she then began receiving a string of messages from her bank.
“In a span of five minutes I was receiving a floodgate of messages from my bank asking me to make certain authorizations. I asked the supposed-to-be customer care agent who was still on the line about the string of messages. He at this point instructed me to put my phone on airplane mode for five minutes ‘so as to restore normalcy’ from their end,” she says.
Unsuspecting and following cues like a loyal customer eager to resolve a service problem, Ruth says she put her phone on airplane mode as was instructed.
“When after five minutes I turned off airplane mode on the device and tried to use my phone to make a phone call, I realized the phone calls were not going through. I realized something was not right and now I could not call back even the landline that I had been on call with just five minutes earler ,” she says, visibly in emotional pain from the harrowing incident.
To her credit, upon realizing something was not right, Ruth Kamau sent out a tweet over the computer to her bank informing the bank of her suspicions of an apparent security breach.
“The bank promptly took action and froze all transactions on the account which was at the time attached to mobile banking.” She told The Times.
She was however not so lucky with a Front Office Savings Account (FOSA) she operated with a local SACCO which she frequently used for mobile banking on her mobile phone number.
“My SACCO FOSA accounts were swept clean. I lost over Ksh90, 000 in a flash. Whoever was behind the criminal back-end activity proceeded to withdraw everything I had on the SACCO FOSA account via MPESA. They also emptied my MPESA account and borrowed Fuliza mobile loans on the line to my maximum limit as at the time. They moved airtime worth Ksh5, 000, which I had in the Safaricom SIM card at the time.” says Ruth Kamau.
Early next morning she woke up after a restless night and made her way in person to report the incident with her mobile phone service provider.
All she got, according to Ruth Kamau, was a reinstatement of her details as the legitimately registered owner of the Sim card.
“I reported this case with Safaricom’s Head of Cyber Security but there has not been much assistance coming forth. I have also reported this incident with the police but the cops are yet to tell me anything to date, she says in visible anguish.
“What I find most frustrating and infuriating, however is the fact that the financial institutions from which I lost money, including the mobile money transfer service provider from which my hard earned money was stolen, in a bid to distance themselves from my losses, now claim that the transactions look like they were made from my end,” she quips, devastated.
Ruth is only one of the thousands of Kenyans who have recently lost their hard earned money to savvy cyber criminals now operating in the country with wanton impunity.
Like many Kenyans, who have been conned of their millions, Ruth is now pointing a direct accusing finger at Safaricom, her mobile service provider, for the security breaches that led to her SIM card being swapped and used for fraudulent transactions to her loss.
Electronic money fraud is a new frontier of crime authorities in Kenya are now arming to fully combat. In late July this year, detectives from the Directorate of Criminal Investigations (DCI) serious crimes unit arrested three suspects who have been defrauding M-Pesa operators across the country.
Jacktone Odhiambo Opondo, Millicent Wanjiru Maina and John Karuku Kabue were arrested in separate locations with over 3,000 Safaricom lines, both registered & unregistered.
“It has been established that the gang has been getting ID numbers from a loans App known as Scoppe, and thereafter using the same to illegally register the acquired sim card,” said the DCI in a statement.
To execute their fraud, the suspects approached Mpesa Agents as dealers in pretext of selling SIM cards & other products at discounted prices, and in the process switched the agents Mpesa phones before flushing their float, according to the DCI.
A week later on August 8, DCI detectives arrested four suspects; two females & two males for the offence of illegal registration of SIM cards. Approximately 30,000 SIM cards, 240 iPhone, 150 MI phones, 2 Laptops, 2 inverters & other electrical appliances were recovered.
Prosecution of cyber criminals in Kenya is yet to result in any precedent-setting convictions, to the detriment of many victims like Ruth Kamau who have lost their hard-earned money in the recent past and who continue to lose their millions to sophisticated latter-day faceless criminals.
Just over a week ago on August 16, A Kibera magistrate’s Court denied DCI detectives 10 more days to hold 5 cybercrime suspects allegedly found in possession of 1720 Safaricom sim cards.
Safaricom getting overwhelmed
According to investigations of The Times, mobile money transfer companies in Kenya, including leading giant telco Safaricom, are fast getting overwhelmed. Just how SIM cards of the company have ended up in so many wrong hands is a puzzle the company is clearly struggling to piece together.
Airtel lines is not spared either. Criminals are taking advantage of Bharti Airtel’s attempt to expand its mobile money transfer footprint across Kenya in a bid to step up competition to the dominant Safaricom MPESA. When DCI detectives arrested five suspects of electronic money in Kasarani within Nairobi County recently, they found the fraudsters in possession of 1,720
unregistered Safaricom lines and 429 Airtel lines.
We reached out to Safaricom for a comment on this story but were yet to receive any comment by the time of going to press.
Instead, the morning after The Times made a request to speak to cyber security heads at the telco, the company sent out a statement informing the public of services interruption specifically affecting activation of new SIM Cards, SIM Swap, PUK and tariff migration lasting twenty four hours between Saturday and Sunday of this past weekend.